CircuitX
A privacy-native perpetual DEX built on Ztarknet
Awards
The problem it solves
Core Problems
- Strategy Exposure & Front-Running
- Lack of Privacy in DeFi Trading
- Vulnerability to Market Manipulation
Our solution
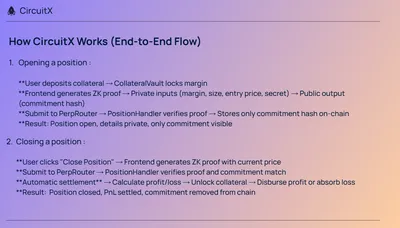
- Complete privacy through ZK proofs. Traders prove position validity without revealing any details. Trade with confidence knowing strategies stay private.
- Position details are cryptographically hidden. Only commitment hashes are on-chain—impossible to reverse-engineer. Traders can execute large positions without revealing strategy or becoming targets.
- Private positions cannot be front-run or targeted. MEV bots cannot see trades, eliminating sandwich attacks and front-running
What People Can Use CircuitX For
Retail Traders
- Strategy Protection: Develop and execute trading strategies without exposure
- Privacy-Conscious Trading: Trade without revealing financial position
- MEV Protection: Avoid front-running and sandwich attacks
- Competitive Advantage: Keep successful strategies private
- Example: A retail trader discovers a profitable arbitrage opportunity. On CircuitX, they can execute it repeatedly without competitors seeing the pattern and copying it.
How CircuitX Makes Existing Tasks Easier/Safer
- No Strategy Management Overhead
- Simplified Risk Management
- Reduced Monitoring
- Strategy Security
Challenges we ran into
Challenges I Ran Into
- Transaction Nonce Mismatch Errors
-
Problem: When calling lock_collateral followed immediately by open_position, the second transaction failed with “Invalid transaction nonce” because the account nonce hadn’t updated on-chain yet
-
Solution: Implemented nonce polling—after lock_collateral confirms, poll the account’s nonce every 500ms until it increments before sending the second transaction. Added a 2-second fallback delay as a safety measure.
- Commitment Format Mismatch (COMMITMENT_MISMATCH Error)
-
Problem: When closing positions, the commitment in the proof’s public inputs didn’t match the commitment parameter passed separately, causing COMMITMENT_MISMATCH errors.
-
Solution: Changed the flow to generate the proof first, then extract the commitment directly from proofResult.publicInputs[1] instead of normalizing the stored position commitment separately. This ensures both commitments match exactly.
- Market ID Format Inconsistencies
-
Problem: Different parts of the system used different formats for market IDs (string vs felt252), causing validation failures.
-
Solution: Created a shared getMarketIdFelt() function to ensure consistent format across the codebase, and removed strict market ID validation since the contract handles format variations internally.